International Journal of Scientific & Engineering Research, Volume 4, Issue 11, November-2013 404
ISSN 2229-5518
1S.G.Santhi, Assistant professor,
Department of Computer Science and Engineering,
Annamalai University sgscse@gmail.com
2Dr.K.Venkatachalapathy
Professor,
Department of Computer Science and Engineering,
Annamalai University
Abstract In this paper, we propose a method to save energy consumption for the rejoin procedure for Cluster Tree in 802.15.4 Sensor Networks .An improved node rejoin procedure has Cluster Head(CH) periodically calculates link quality (LQ) and broadcasts to its child nodes. By receiving LQ value, it stores in its Neighbor Quality (NQ) table. W hen a node lost its connection with its parent
node, it selects the suitable parent node with high link quality. W hen two nodes have similar LQ value, it selects the suitable
parent in terms of tree depth value. This process is completed by processing network response and reply message. Our rejoin procedure conserves more energy and incurs low delay.
Keywords: IEEE802.15.4, Sensor Networks, Cluster Head (CH), Link Quality (LQ), Neighbor Quality (NQ) .
![]()
The wireless network with minimum data rate, reduced energy consumption and minimum cost is formed by IEEE
802.15.4 standard. The distinctive characteristics of the standard makes it more approving module for wireless sensor networks and remote monitoring applications. The physical layer and medium access control layer of data link layer are the lowermost layers of the protocol that is defined by the standard. [1] It offers a minimum power, economic and a consistent protocol for wireless connectivity among low-cost, permanent and moveable devices. These devices can figure out into a sensor network or wireless personal area network (WPAN) [2]. The network holds two categories of the devices such as full function devices (FFD) and reduced function devices (RFD). FFD functions as a router. It is capable of linking to other FFD and RFD devices. RFD has capability to link with FFD devices. [3] IEEE 802.15.4 is utilized to interlink minimum cost sensors, actuators and processing devices in the wireless manner. The several applications of 802.15.4 devices includes industrial control, environmental and health monitoring, home automation, entertainment and toys, security, location, and asset tracking, emergency and disaster response[4].
The most hopeful minimum span wireless
communication technology corresponds to Bluetooth that is depended on time-division multiple access (TDMA) and frequency hopping spread spectrum (FHSS). The main features such as interference flexibility and power efficiency are possessed by this network that is required by
the wireless sensor networks [5]. The ultimatum of portability of mobile connections has resulted in the recurrent raise of attention for Bluetooth wireless personal area network (WPAN) technology. It offers new personal technology. It offers new personal communication prospects and services. [6] In relation to Bluetooth, several communication services can be offered by various WPAN frameworks. It can be interlinked to facilitate allocation of information. In addition, it permits communications with the physical environment. The devices that utilize Bluetooth become Pico nets. It performs the communication in slave-master-slave prototype. A Pico net possesses one master device and seven active slave devices. [6]
The merit of setting up Bluetooth is that the individual
channel are utilized by all the sensor nodes in the radio range for preventing the interference and fight for a shared channel. In addition, the minimum power feature of Bluetooth permits the radio to penetrate the power saving mode when there is lack of dynamic communication. The problem of Bluetooth based sensor network lies in maintaining effective scatter net configuration and in performing routing for a multi-hop network. The simultaneous route discovery performed by the multiple sources can result in complexity. [5]
Li-Hsing Yen et al. [9] have proposed a ZigBee- compliant, distributed, risk aware, probabilistic beacon
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 11, November-2013 405
ISSN 2229-5518
scheduling algorithm. Their proposed algorithm permits a node to assess locally the risk of slot reuse, and based on the assessed risk it adopts the slot with the lowest latency to its parent. They have predicted such a risk as risk probability, that is, the probability that slot reuse between two nodes will cause beacon collisions as seen by a future joining node. To assess this risk probability, they classify pairs of nodes that are at most two hops apart into Inhibited Pairs (IPs), Visible Pairs (VPs), Hidden Pairs (HPs) and Uninhibited Pairs (UPs); and according to the pair type, calculate the corresponding risk probability.
Zdenˇek Hanz´alek et al. [16] have proposed a Time
Division Cluster Scheduling (TDCS) mechanism. Their
proposed scheme is constructed based on the cyclic
extension of RCPS/TC (Resource Constrained Project Scheduling with Temporal Constraints). It is a problem for a cluster-tree WSN and it assumes bounded communication errors. It is designed to meet all end-to-end deadlines of a predefined set of time-bounded data flows while minimizing the energy consumption of the nodes by setting the TDCS period as long as possible. Since each cluster is active only once during the period, the end-to-end delay of a given flow may span over several periods when there are the flows with opposite direction. Theie scheduling mechanism assists system designers to efficiently configure all required parameters of the IEEE
802.15.4/ZigBee beacon-enabled cluster-tree WSNs in the
network design time.
Anis Koubâa et al. [17] have introduced a scheduling
mechanism that utilized Time Division Beacon Scheduling
approach (TDBS). It is presented for building a ZigBee cluster-tree WSN based on a time division approach. More importantly, their proposed TDBS mechanism can easily be integrated in the IEEE 802.15.4/Zig-Bee protocol stack with only minor add-ons. Initially, they have identified and analyzed the beacon frame collision problem, and the different approaches proposed in Task Group. Futher, they have also proposed a beacon frame scheduling mechanism (TDBS) based on the time division approach to build a synchronized multi-hop cluster-tree WSN. Finally, they have concluded by introducing a duty-cycle management methodology for an efficient utilization of bandwidth resources in the cluster-tree network.
Ismail Salhi et.al [18] have presented a CoZi, which is a
new packet scheduling mechanism for large scale ZigBee
networks. CoZi aims at enhancing the reliability of the data
delivery and the bandwidth utilization of the network. Their scheduling mechanism entirely based on simple network coding at intermediate nodes to offer better bandwidth utilization and reliable communications with extremely negligible network overhead. Using clever topology inferring from ZigBee signalization messages, this mechanism helps to perform more optimized coding decisions in order to allow a larger range of decoding nodes whether for routed or dissemination based ZigBee sensor networks. CoZi can be included in sleep-awake mechanisms for better energy efficiency.
Mohamed k. Watfa et al. [19] have proposed a novel scheduling algorithm for WMSNs. Their algorithm divides the frame sent from the cluster-head to the Base Station (BS) into slots and gives a percentage of these slots into each node. The base station (BS) sends a certain query to the cluster-head. Upon receiving query, the cluster head will propagate it to specified nodes and wait for these nodes to sense the medium and come back with needed data. The nodes will respond by sending packets of data to the cluster-head. The job of the cluster head is to schedule these packets coming from different nodes to send them in frames to the BS. One of the advantages of this algorithm is that it is derived for a multi-user network and it is shown to converge to the optimal schedule. Another advantage is that the setting is realistic and thus it is feasible.
Each node maintains a neighbor quality table (NQ) (as per equation-3) for its neighboring node. The NTQ table is used by each node to keep tracks the quality of each node. The NQ table contains the neighboring node ID, sequence number, duration field, LQ value and possible parent. Here, the duration field refers to the time interval since a last link quality status is received. This field is maintained to check the newness (freshness) of link quality. The field possible parents can be any neighboring node that a node wants to join with it after it disconnects the connection with previous parent. The header format of NQ table is given below,
Table 1: Header of NQ Table
Neighbor Node ID | Sequence Number | Link Quality (LQ) | Duration | Possible Parents |
Each cluster head (CH) periodically estimates and broadcasts the LQ of its child nodes. By receiving the LQ value, each node updates its neighbor table. When the parent node is out of power and failed, the child nodes of corresponding parent trigger the rejoin procedure to find suitable parent to connect with the coordinator. Let ni be node i, where i = {1, 2 ... n} The rejoin procedure of a node is as follows,
(i) When node i lost connection with his parent node it
triggers rejoin procedure
(ii) It looks NQ table and finds all neighboring nodes
that exist within its transmission range.
(iii) The field possible parents can be constructed by
choosing the nodes with latest duration field.
(iv) The chosen possible parents’ nodes are stored in
NQ table for selecting suitable parent node.
(v) From stored possible parent nodes, ni selects the node with high LQ value
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 11, November-2013 406
ISSN 2229-5518
(vi) When more than one node has similar LQ value then the further parent node selection(vi) When more than one node has similar LQ value then the further parent node selection is based on depth of a node in the tree structure.
(vi) The node with low depth is elected as suitable
parent
(vii) After the selection of suitable parent, node ni
transmits Nwk-Join (Network Join) message to the
selected suitable parent.
Nwk − Jin
The performance of the proposed Rejoin Procedure for Multiple Cluster Tree (RPMCT) is evaluated using NS2 [21] simulation. A network which is deployed in an area of 50 X
50 m is considered. The IEEE 802.15.4 MAC layer is used
for a reliable and single hop communication among the
devices, providing access to the physical channel for all
Node ni
→ Suitable Parent
types of transmissions and appropriate security
(viii) While receiving the Nwk-Join message, the suitable parent node transmits back the Nwk-Res (Network Response) message to the corresponding node.
Nwk −Re s
mechanisms. The IEEE 802.15.4 specification supports two
PHY options based on direct sequence spread spectrum (DSSS), which allows the use of low-cost digital IC realizations. The PHY adopts the same basic frame structure for low-duty-cycle low-power operation, except
Node ni
← Suitable Parent
that the two PHYs adopt different frequency bands: low-
(ix) By receiving the Nw-Res message, node ni joins with the selected parent
(x) If node ni does not receive the Nw-Res meassge even after the time interval of Ires , the
corresponding repeat the same process again to
find the suitable parent.
Consider the scenario given in figure-1; we can observe that node n7 lost its connection with its parent node n5; this disconnection may be due to the failure of node n5. After
the failure of n5, node n7 invokes the rejoin process. It has
four successful neighbor nodes in its NQ table. By considering duration time, n7 selects 8, 6 and 9 as possible parents. After checking LQ value of three nodes, n7 found that n6 and n8 has similar high LQ value than n9. Now, it selects node n8 as its suitable parent by considering depth value. Using Nwk-Join and Nwk-Res messages, n7 joins with n8.
band (868/915 MHz) and high band (2.4 GHz). The PHY layer uses a common frame structure, containing a 32-bit preamble, a frame length.
The simulated traffic is CBR with UDP source and sink. Table 2 summarizes the simulation parameters used.
Table 2: Simulation Parameters
No. of Nodes | 21,41,61,81 and 101 |
Area Size | 50 X 50 |
Mac | IEEE 802.15.4 |
Simulation Time | 20,40,60,80 and 100sec |
Transmission Range | 12m |
Routing Protocol | RPMCT |
Traffic Source | CBR |
Packet Size | 80 bytes |
The performance of RPMCT is compared with the Risk- Aware Beacon Scheduling (RABS) protocol [9]. The performance is evaluated mainly, according to the following metrics.
Energy Consumption: It is the average energy consumed by the nodes for the transmission process.
The simulation results are presented in the next section.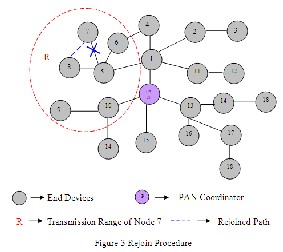
In our first experiment we vary the number of nodes as
21,41,61,81 and 101.
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 11, November-2013 407
ISSN 2229-5518
3.05
Energy3(J)
2.95
2.9
2.85
Nodes Vs Energy
21 41 61 81 101
Nodes
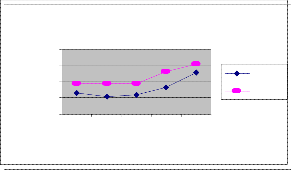
Figure 1: Nodes Vs Energy
RPMCT RABS
[1] H. Fariborzi, M. Moghavvemi, “EAMTR: energy aware multi-tree routing for wireless sensor networks”, IET Communication, Vol. 3, Iss. 5, pp. 733–739, 2009.
[2] Gurjit Kaur, Kiran Ahuja, “Qos Measurement of Zigbee Home Automation Network using Various Routing Protocols”, International Journal of Computer Applications, Volume 13– No.2, pp.25-30,Jan 2011.
[3] M. Al-Harbawi, M. F. A. Rasid, N. K. Noordin, “Improved Tree Routing (ImpTR) Protocol for ZigBee Network”, IJCSNS International Journal of Computer Sci 146 ence and Network Security, VOL.9
No.10,pp.146-152, Oct.2009.
[4] Francesca Cuomo, Sara Della Luna, Ugo Monaco,
Tommaso Melodia, “Routing in ZigBee: benefits from
From figure 1, we can see that the average energy consumption of our proposed RPMCT is less than the existing RABS protocol.
In our second experiment we vary the simulation time as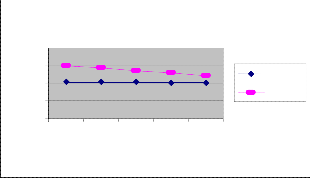
20,40,60,80 and 100 sec.
Time Vs Energy
En 4 y(J)
exploiting the IEEE 802.15.4 association tree”, pp. 3271-
3276, 2007.
[5] Xin Zhang, George F. Riley, “An On-Demand Bluetooth
Scatternet Formation and Routing Protocol for Wireless
Sensor Networks”, Proceedings of the Sixth
International Conference on Software Engineering, Artificial Intelligence, Networking and Parallel/Distributed Computing and First ACIS International Workshop on Self-Assembling Wireless Networks, 2005.
[6] Yuh-Shyan Chen and Tsung-Hung Lin, “A time-slot leasing-based QoS routing protocol over Bluetooth
erg
3
2
1
0
20 40 60 80 100
Time(Sec)
Figure 2: Time Vs Energy
RPMCT RABS
WPANs”, Int. J. Ad Hoc and Ubiquitous Computing, Vol. 2, No. 1/2, 2007.
[7] Petr Jurcik, Anis Koubaa, Mario Alves and Eduardo
Tovar, “On the Capacity of Cluster-tree ZigBee
Networks”, 12-15-2009
[8] Petr Juric, Anis Koubaa, Ricardo Severino, Mrio Alves
and Eduardo Tovar, “Dimensioning and Worst-case
Analysis of Cluster-Tree Sensor Networks”
[9] Li-Hsing Yen, Yee Wei Law, and Marimuthu
Palaniswami, “Risk-Aware Distributed Beacon Scheduling for Tree-Based ZigBee Wireless Networks”, IEEE Transactions on Mobile Computing, pp- 692 –
703, 2012
From figure 2, we can see that the average energy
consumption of our proposed RPMCT is less than the
existing RABS protocol.
.
In this paper, we have proposed a rejoin procedure for cluster tree in Zigbee sensor networks. In this technique, an improved rejoin procedure is used to select the suitable parent considering link quality indicator. The rejoin procedure reduces time delay and energy consumption by avoiding rescanning of entire network. Through simulation results, the proficiency of our technique has proved. Our technique conserves more energy and incurs low delay.
[10] John A. Stankovic,” Wireless Sensor Networks”, ieeexplore.ieee.org June 19, 2006.
[11] Gurjit Kaur, Kiran Ahuja, “QoS measurement of Zigbee
home automation network using various modulation
schemes” International Journal of Engineering Science
and Technology (IJEST) ISSN: 0975-5462 Vol. 3 No. 2
Feb 2011
[12] Yuh-Shyan Chen and Tsung-Hung Lin, “A time-slot
leasing-based QoS routing protocol over Bluetooth
WPANs”, Int. J. Ad Hoc and Ubiquitous Computing,
Vol. 2, Nos. 1/2, 2007.
[13] Jin-Seok Han, Hyung-Sin Kim, Jae-Seok Bang and
Yong-Hwan Lee, “Interference Mitigation in IEEE
802.15.4 Networks”.
[14] Chiara Buratti, Andrea Conti, Davide Dardari and
Roberto Verdone, “An Overview onWireless Sensor
Networks Technology and Evolution”, Sensors, 2009
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 11, November-2013 408
ISSN 2229-5518
[15] S.G.Santhi and K.Venkatachalapathy, “Ant based Multiple Cluster Tree Routing for 802.15.4 Sensor Networks”, International Journal of Computer Applications, Volume 48– No.10, June 2012
[16] Zdenek Hanzalek and Petr Jurcik, “Energy efficient
scheduling for cluster-tree Wireless Sensor Networks
with timebounded data flows: application to IEEE
802.15.4/ZigBee”, 05-05-2010.
[17] Anis Koubâa, André Cunha, Mário Alves and Eduardo
Tovar, “TDBS: a time division beacon scheduling mechanism for ZigBee cluster-tree wireless sensor networks”, Springer, 2008.
[18] Ismail Salhi, Yacine Ghamri-Doudane, Stéphane Lohier and Erwan Livolant,” Cozy: basic Coding for better
Bandwidth Utilization in ZigBee Sensor Networks”, IEEE GLOBECOM, (2010).
[19] Mohamed K. Watfa, Farah Abou Shahla. “Energy- efficient scheduling in WMSNs”, vol. 8, no. 1, pp 45-54,
2009
[20] Michele Rondinone, Junaid Ansari, Janne Riihijarvi and Petri Mahonen, “Designing a Reliable and Stable Link Quality Metric for Wireless Sensor Networks”, Proceedings of the workshop on Real-world wireless sensor networks (REALWSN '08), pp 6-10, 2008.
[21] Wangang Wang and Yong Peng, "An Improved
Routing Algorithm for ZigBee Networks", International Review on Computers and Software (IRECOS), September 2012,Vol. 7 N. 5 (Part B),pp. 2321-2325
[22] Nidal Abid and Al-Hamid Al-Dmour, "Studying the
Effect of Varying Time Slots Allocated for GTS on IEEE
802.15.4 Performance", International Review on
Computers and Software (IRECOS), September
2011,Vol. 6 N. 5, pp. 806-810

[23] Network Simulator: http:///www.isi.edu/nsnam/ns
S.G.SANTHI obtained her Bachelor’s degree in Computer Science & Engineering from Mookambigai College of Engineering, Bharathidasan University, Tamilnadu, India in
1992.Then she obtained her Master’s
degree in Computer Science &
Engineering from Annamalai University, Tamilnadu, India in
2005.She is currently working as an Assistant Professor in the Department of Computer Science & Engineering, Faculty of Engineering & Technology, and Annamalai University. She is having 14 years and 2 months of experience in teaching. She has published more than 10 Research papers in International & National Conferences. Her field of interest includes Computer Networks. She is a life member in various professional bodies like ISTE, CSI. Etc.
1987 and he received his Master’s degree in Computer Applications from Pondicherry University in 1990. He completed his Ph.D in Computer Science & Engineering from Annamalai University, Tamilnadu, India in 2008. He is currently working as Professor in the Department of Computer Science & Engineering, Faculty of Engineering &
Technology, and Annamalai University. He is having 19 years
of experience in teaching. He has published more than 20 research papers in international conferences and journals. His field of interest includes Image Processing and Computer networks. He is currently guiding 8 research scholars towards Ph.D. He is a life member in various professional bodies like ISTE, CSI. Etc.,

IJSER © 2013 http://www.ijser.org