International Journal of Scientific & Engineering Research, Volume 4, Issue 4, April 2013
ISSN 2229-5518 1587
Improving Security & QoS in IP-Based
MANETs
Talwinder Singh , Anurag Singh Tomar
Abstract-A mobile ad hoc network (MANET) is a temporary network formed by the collection of mobile nodes. The network formed do not require any physical infrastructure. There is no central authority to administer the services and configurations of the network. Securing MANETs is still an active area of research. In this paper, we propose the use of security mechanisms to improve t he security as well as QoS in MANET. A combination of different parameters will be considered to compute optimal path from source to destination and use a simple key agreement scheme that is based on the Station-to-Station key agreement protocol.
Index Terms:- Energy level , Hop count , Key Management, MANET Security, QoS, Symmetric Encryption Keys , Station-to-Station
Key agreement
1. INTRODUCTION
The spontaneous grow th of technology for mobile devices, including laptops and computers, and the availability of cheap w ireless netw orking [1] hardw are, has resulted in a great demand for w ireless connectivity among mobile users. One approach to providi ng w ireless connectivity is through the formation of a mobile ad hoc netw ork .
A mobile ad hoc netw ork (M A N ET) [1] is a collection of mobile nodes that tempor arily integrate to form a netw ork. Such type of netw ork does not require the use of the typical i nfrastructure underlying a netw ork. Rather, each mobile node is equipped w ith a w ireless interface that allow s the node to communicate w ith other nodes via the w ireless medium. H andheld computing devices and laptop computers w ith w ireless transceivers are examples of mobile nodes that can come together to form a M A N ET. In a M A N ET, there is no central entity w ith the authority to administer the services and configurations of the netw ork. A ll the nodes w ork collectively and cooperatively, in a
that can achieve broad protection w ith desirable netw ork performance.
2.1 Session key generation A lgorithm
Dif f ie-H ellman Key Agreement :- It w as the f ir st pract ical key dist r ibut ion [1] and creat ion protocol that per mit ted t w o communicat ing ent it ies to create a shared key by exchanging infor mat ion through an open channel, w ithout requir ing any pr ior know ledge to be shared among them . This solut ion is a per fect match for the issues involved in for ming a M A N ET. The secur it y of this protocol is based on the comput at ional hardness of the Dif f ie-H ellman probl em and its related problem of calculat ing discreet logar ithms .The Dif f ie-H ellman protocol w orks as foll ow s
A ssumptions:-
G is a finite cyclic group w ith a generator g.
A and B are tw o entities w ho w ant to establish a shared secret key.
Steps: -
1) A chooses a large random number x such that
0<x<p-1 and calculate R =gx mod p
2) B chooses a large random number y such that
y
distributed manner, to maintain the functions and ser -
vices of the netw ork. The distr ibution of responsibilities and tasks that are meant to keep the
0<y<p-1 and calculate R2= g
3) A sends R1 to B ,.
4) B sends R2 to A
mod p
netw ork running makes the netw ork resilient to node
5) A calculates K=(R )x mod p.
y
failures. It also allow s nodes to join and leave the
6) B calculates K=(R1)
mod p.
netw ork liberally w ith- out affecting the netw ork ’s operability.
2. LITERATURE SURVEY
Security has become a pri mary concern in order to provide protected communication betw een mobile
7) Values of keys should be same.
2.2 Weakness in Deffie H ellman A lgorithm
The Deffie-H ellman key exchange is susceptible to tw o attacks:-
Discrete Logarithm A ttack :- The security of key exchange is based on the difficulty of the logarithm
nodes in a dynamic environment. Unlike the w ired
problem . Third person can intercept R and R
If third
1 2.
netw ork, the unique features of mobile ad hoc netw orks
person can find x fr om R = gx mod p and y from R = gy
1 2
pose a number of nontrivial challenges to security
design, like open peer -to-peer netw ork architecture, shared w ireless medium, resource constraints, and dynamic netw ork structure. These characteristics clearly make a case for building multi -fence security solutions
mod p then he can calculate the symmetric key K= gxy
mod p . Thus secret key is not anymore secret.
M an-in-middle A t t ack:- The attacker bet w een A and B
do not need to f ind the values of x and y to att ack . H e
IJSER © 2013
IhJttSp:E//wRww©.ijs2e0r.1or3g
http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 4, April 2013
ISSN 2229-5518 1588

can easily fool A and B by creat ing t w o keys : one be

bet w een himself and A , and another bet w een himself B
and B. In this w ay this at tack can be successf ul. B is C


fooled into believ ing that the message has come f rom A
and similar scenar io can happen to A in other di rect ion. D G

3. ISSUES AND DIFFICULTIES IN MANETS A M A N ET i s dif ferent f rom the convent ional w ired

net w orks. This dif ference int roduced few dif f icult ies in

achiev ing Qualit y of Ser v ice in such net w orks. The F
foll ow ing are the problems :- E
Dynamic N et w ork topologies:- N odes can move f reely, thus, the net w ork topology[3] w hich is t ypically mult i - hop - may change randomly and rapi dly at unpredict able t imes, and may consist of both bidirect ional and unidirect ional links.
Bandw idth-const rained, var iable capacit y links:- Wireless links w ill cont inue to have signif icant ly low er capacit y then w ired one. In t ur n, the measured throughput of w ireless communicat ions - af ter account ing for the ef fects of mult iple access, fading, noise, deter iorat ion and inter ference condit ions ,etc.- is of ten much less than a radio’s maximum t ransmission rate. So, ef fect of the relat i vely low to moderate link capacit ies is that congest ion is t ypically the nor m rather than the except ion, i.e. tot al applicat ion demand w ill likely approach or exceed net w ork capacit y f requent ly . A s the mobile net w ork is of ten simply an advancement of the f ixed net w ork inf rast r uct ure, mobile ad hoc user s w ill demand same ser v ices.
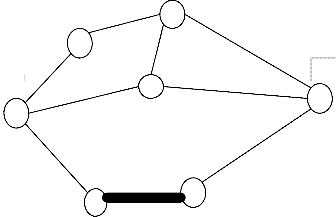
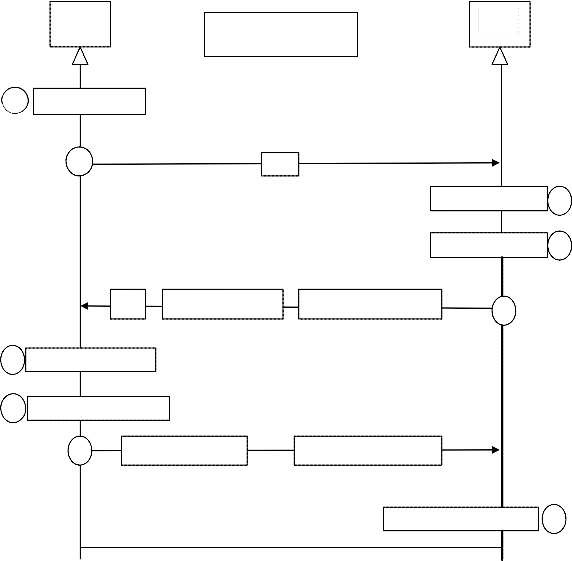
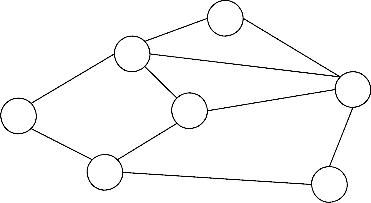
Fig :- 1 Mobile Nodes
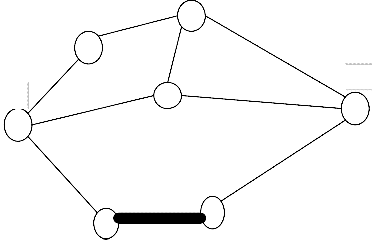
STEP :- 2 A f ter select ing source and dest inat ion , nodes w ithin the def ined range w ill join together to for m a net w ork and star t exchanging rout ing infor mat ion w ith each other.
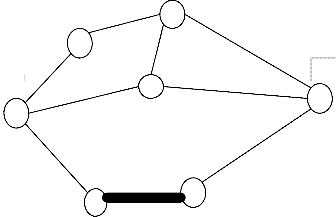
C B
D
G A
F
Energy-const rained operat ion:- Some or all of the nodes E
in a M A N ET may rely on bat ter ies or other exhaust ible
means for their energy. For these nodes, the impor t ant system design scheme for opt imizat ion may be energy conser vat ion.
Fig:-2 M obile nodes creat ing a net w ork
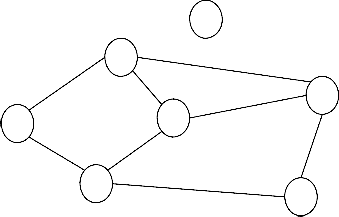
STEP:- 3 Path Sel ecti on and Route Computati on
+2
+3 C
4. OUR PROPOSED MACHNISMS FOR
B
SECURITY AND QoS:-
+5
STEP :- 1 Creation of netw ork :- +2 D
G
There are number of mobile nodes roaming freely and A +4
independently. A specific range w ill be defined for the node to be the part of the netw ork . if the node comes in the defined range then it w ill join the netw ork.
F
+3 E +2
Fig :-3 M obile ad-hoc net w ork w ith energy level s
IJSER © 2013 http://www.ijser.org IJSER © 2013
http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 4, April 2013
ISSN 2229-5518 1589
Table :- 1
Source | Dest inat ion | Possible Path | H op Count | Energy level |
A | G | A-B-C-G A-D-C-G A-B-C-D-G A-D-G A-E-F-G | 3 3 4 2 3 | 12 13 16 11 12 |
In the given diagram w e have source node A and
Dest inat ion node G. H ope count and Energy level are L
the only t w o parameter s consi dered in this scenar i o .
We have dif ferent paths f r om source to dest inat ion:-
A -B-C-G A
A -D-C-G
A -B-C-D-G D
A -D-G [Least H op count]
A -E-F-G S E
Fir st of all w e w ill choose path w ith least hop count and check if there is any node i n this path w ith 0 and +1 energy level. if node w ith 0 and +1 energy level exist then w e w ill simply sk ip this path and select the 2nd path w ith least hop count. Repeat the same process and send the dat a through the best selected path.
Path Selected: - A-D-G
While sending data from source to destination various parameters are considered to compute path , for example :- hop count , energy level , trust level etc.
In our proposed solution, w e w ill calculate path from source to destination by using tw o factors together, i.e hop count and energy level.
H op count w ill calculate the shortest path w hile energy level w ill help us in calculating the path through those nodes w hi ch has high energy level. In this w ay the optimum path w ill be considered for sending data. M oreover , it w ill eliminate the problem of data loss due to link breakage in M A N ETs.
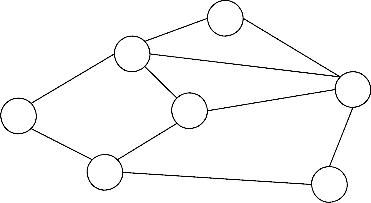
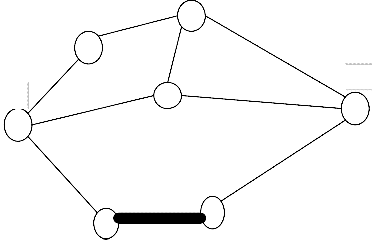
STEP: - 4 Condition w hen a N ode goes out of range
In the given diagram node L is going out of range and it w ill leave the netw ork. N ow , nodes w ill again exchange informati on w ith each other and update their tables accordingly.
C
F
Fig :- 4 M obile node going out of range
STEP :- 5 Condition w hen a new node join the netw ork
When a new node join the netw ork , again all the nodes in the netw ork w ill exchange information w ith each other and update their tables accordingly
L A
D S E
C
F
Fig :-5 N ew node joini ng the net w ork
IJSER © 2013 http://www.ijser.org IJSER © 2013
http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 4, April 2013
ISSN 2229-5518 1590
STEP :- 6 Session key generation algor ithm
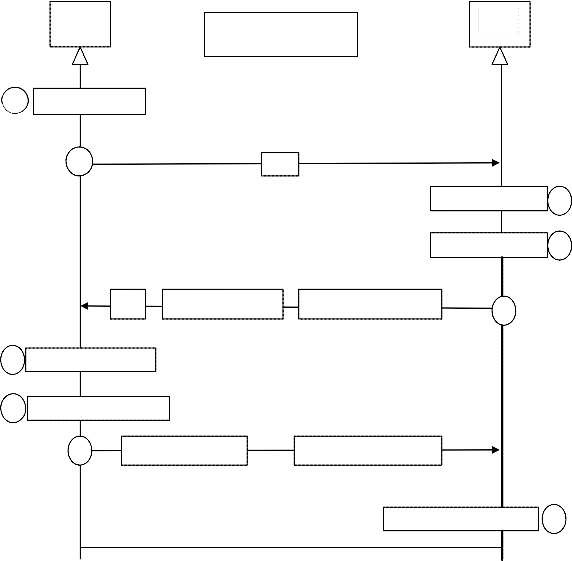
Aman
Ben
PC The values of p and g are PC
public
1 R = gx mod p
2 R1
R2 = g
mod p 3
K = (R )y
Ks
mod 4
R2 Ben’s certificate
SigBen (Aman|R1|R2)
5
6 K = (R )x mod p
Signed by Ben’s Private Key
7 Verify Ben’s signature
s
8 Aman’s Certificate SigAman(Ben|R1|R2)
Signed by Aman’s Private
Verify Aman’s Signature 9
Shared secret Key
K= gxy mod p
Fig :- 6 St at ion-to-St at ion key agreement in M A N ETs
In our proposed mechanism w e are using Station-to- Station key agreement [14] to deal w ith the problems in Deffie H ellman key agreement. This method use digital signature w ith public-key certificates to establish a session key betw een A and B. Thi s method provides integrity as w ell as authentication .
We have implemented stati on-to-station key agreement in M A N ETs for generating session key and thus pr ovide secure communication. A fter generating secret key w e can encrypt the text using any of the encr yption algorithm w ithout affecting the overall QoS.
IJSER © 2013 http://www.ijser.org IJSER © 2013
http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 4, April 2013
ISSN 2229-5518 1591
Descri ption in steps
Suppose A man = A and Ben = B
1) A fter calculating R1 , A sends R1 to B.
2) A fter calculating R2 , and session key , B
concatenates A ’s ID , R1 and R2. H e then signs
the result w ith hi s private key. B now sends R2 ,
the signature and hi s ow n public key
certificate to A . The signature is encrypted w ith the session key.
3) A fter calculating the sessi on key , if B’s Signature is verified , A concatenates B’s ID , R1 and R2 . H e then signs the result w ith his ow n private key and sends it to B. The signature is encrypted w ith session key.
4) If A ’s Signature is verified , B keeps the session key
Key agreement w ill be bet ween source and dest inat ion only (end to end) and to avoid comput at ion overheads only the payload por t ion w ill be encr ypted .
5. STRENTH OF PROPOSED SOLUTIONS:-
The Station-to-Station key agreement prevents man-in- middle attacks . A fter inter cepting R1, attacker cannot send hi s ow n R2 value to A and pretend it is coming from B because attacker cannot forge the private key of B to create the Signature – the signature cannot be verified w ith B’s public key defined in the certificate . In the same w ay, attacker cannot forge A ’s private key to sign the third message sent by A .
Link breakage is one of the major problem in M A N ETs because of the mobility of nodes or pow er available in each node. In our pr oposed solution w e have removed the problem of link breakage by considering energy level of every node in the ad-hoc netw ork.
6. CONCLUSIONS
In this paper w e created session key using Station-to-
station key agreement. This key w ill be used in M A N ETs for secure communication. The M obile ad - hoc netw ork is open to everyone so security is one of the important concern in M A N ETs. Various other methods can be used to encrypt the message after generating the session key . Security can be improved further but keeping the computation overheads normal.
There many other parameters such as tru st level , bandw idth , route repetition etc . These parameters can also be combined to improve the overall QoS in M A N ETs.
7. Acknowledgements
M y si ncere thanks to my honourabl e guide and other s w ho have contr i buted tow ards the preparati on of the paper.
8. REFRENCES
[1]. A bdul rahman H . A l tal hi , “A Si mpl e Encrypti on Keys Creati on Scheme i n Wi rel ess A d H oc N etw orks” , Sci enti fi c Research Publ i shi ng
w w w .sci r p.or g/ jour nal / PaperDow nl oad .aspx?D OI=10.4236/ cn
[2]. Peter J. J. M cNer ney and N i ng Zhang , “Tow ards an Integrati on of Secur i ty and Qual i ty of Ser v i ce i n IP-Based M obi l e Ad Hoc Netw orks” , IEEE Gl obecom 2011 http://ieeexplore.ieee.org/xpl/articleDetails.jsp?rel oad=true&arnumber=6133684&contentType=Con ference+Publications
[3] Ji anbo Xue , Dr. Gustavo A lonso , “Qual i ty of
Servi ce for M obi l e A d H oc N etw orks” , ETH SFT
2003
http:/ / i jar csee.or g ›/ H ome/ Vol 1, N o 7 (2012)
/ Pand a
[4]. H . Yang, H . Luo, F. Ye, S. Lu and L. Zhang, “Securi ty i n M obi l e A d H oc N etw orks: Chal l enges and Sol uti ons,” IEEE Wi rel ess Communi cati ons,.
d oi :10.1109/ M WC.2004.1269716
[5] G.S. M amatha , Dr. S.C. Shar ma , “Netw ork Layer A ttacks and Defense M echanisms i n M A N ETS- A Sur vey” , Inter nati onal Jour nal of Computer A ppl i cati ons www.ijcaonline.org/volume9/number9/pxc387191
1.pdf.
[6] Suni l Taneja and A shw ani Kush , “A Sur vey of Routi ng Protocol s i n M obi l e Ad Hoc Netw orks” , Inter nati onal Jour nal of Innovati on, M anagement and technol ogy
http:/ / www.minema.di.fc.ul.pt/report_routing- protocols-survey-final.pdf
[7] PRA DIP M . JAWA N DH IYA , “A Sur vey of M obi l e Ad Hoc Netw ork A ttacks” , Inter nati onal Jour nal of Engineer ing Sci ence and Technol ogy www.ijest.info/docs/IJEST10-02-09-22.pdf
[8] R. N oval es and N . M i ttal , “Parameterized Key
A ssi gnment for Confi denti al Communi cati on i n Wi rel ess N etw orks,” A d H oc N etw orks, Vol . 9, N o. 7, 2011, pp. 1186-1201. d oi :10.1016/ j.ad hoc.2011.01.009
[9] J. Lee and D. R. Sti nson, “On the Constructi on of Pra- cti cal Key Predi stri buti on Schemes for Di stri buted Sensor N etw orks Usi ng Combi natori al Desi gns,” A CM Trans- acti ons on
IJSER © 2013 http://www.ijser.org IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 4, April 2013
ISSN 2229-5518 1592
Informati on and System Securi ty (TISSEC), Vol .
11, N o. 2, 2008, pp. 1-35. d oi :10.1145/ 1330332.1330333
[10] S. Capkun, J. H ubaux and L. Buttyan, “M obi l i ty H el ps Peer -to-Peer Securi ty,” IEEE Transacti ons on M obi l e Computi ng, Vol . 5, N o. 1, 2006, pp. 43-
51. d oi :10.1109/ TM C.2006.12
[11] E. Bresson, O. Chevassut and D. Pointcheval , “The Group Di ffi e-H el l man Probl ems,” In: K. N yberg and H . H eys, Eds., 9th A nnual Internati onal Workshop on Se-l ected A reas i n Cryptography (SA C’02), Spri nger -Verlag, London, 2002, pp. 325-338.
[12] E. N gai, M . Lyu and R. Chin, “A n A uthenti cati on Servi ce agai nst Di shonest Users i n M obi l e A d H oc N etw orks,” Proceedi ngs of the 2004 IEEE A erospace Conference, Big Sky, Vol . 2, 6-13
M arch 2004, pp. 1275-1285.
[13] S. Zhu, S. Xu, S. Seti a and S. Jajodi a, “LH A P: A Li ght-w eight N etw ork A ccess Control Protocol
for A d H oc N etw orks,” A d H oc N etw orks, Vol . 4, N o. 5, 2006, pp. 567-585. d oi :10.1016/ j.adhoc.2006
Books :-
[14] Behrouz A . Forouzan, Debdeep M ukhopadhyay , cryptography and netw ork securi ty second edi ti on M c graw H i l l (2010).
IJSER © 2013 http://www.ijser.org IJSER © 2013 http://www.ijser.org