International Journal of Scientific & Engineering Research, Volume 4, Issue 8, August-2013 1885
ISSN 2229-5518
Abstract-Some web-based email services are examples of cloud computing carrying into effect. Other illustrations are web-based document warehousing, edit out and collaboration tools. Cloud computing table services are also apply for web- commerce .The cloud computing extend vast opportunities to the IT industry, the growing of cloud computing. Cloud computing focal point on delivery of authentic, faster, fault
tolerant, 24/7 support, sustainable of cloud computing base structures for hosting internet- based application services. This application has different composition, conformation and strategic positioning requirements. Technology is currently at its beginning, with many points still to be referred. Cloud computing has recently developed as a new pattern for hosting and giving services. Cloud computing is obtaining democratic and IT giants such as Google, Amazon, Microsoft, IBM have started their cloud computing sub structure.
Keywords: Cloud computing, sustainable, fault tolerant, web-commerce, documents warehouse, information technology
their details from other clients, and to construct it show to customers that they are the only user of a divided computer or software application.
present computer transforming, storage and network bandwidth as request by customer requirement.
associates customers only paying for the
computing resources that they actually purpose, and being able to recorder their control.
and smart‐phones.
using divided computing resources to permits cloud services to among clients. Virtualisation
and multi‐tenancy supports are typically used
to both differentiate and cover each client and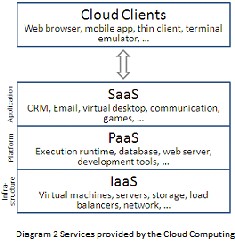
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 8, August-2013 1886
ISSN 2229-5518
and interchangeable services over the web . An example of IaaS is cloud storage, which provides users access to scalable online storage.
complete application is offered to the client as
a table service on their requirement, applications both world-wide, such as word processing, email and spreadsheet, specify such as customer relationship management (CRM) and enterprise resource management (ERP).
organizations and maintains a particular association that has a divided tasks and targets, security Requirements, policies, and
compliance considerations. An example is
Google Gov.
company and it is managed solely for that company. Intel, Hewlett Packard and Microsoft keep their
own internal private clouds.
structure contains of two or more clouds
(public,
Community, or private) that stay singular
existences but are limit together by similar or
proprietary technology that permits data or application portability.
4.2 ElasticityE: lasticity profits obtain from quick provisioning of latest volume and quick relocation of workloads. In public sector sites, cloud computing requires agility in position of procurement and attainment process.
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 8, August-2013 1887
ISSN 2229-5518
only be provisioned, but also de-provisioned
in a highly technology trades. This precise quality approaches critical productivity to enterprises.

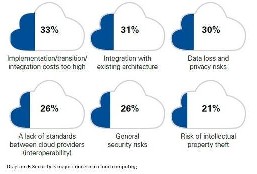
6.1 Data security
Data protection is a important component that permits analyse. companies are unwilling to purchase an guarantee of industry data assurance from suppliers. They worry missing data to challenge and the data secrecy of customers. In among cases, the real storage site
is not discovered, including onto the assurance
affects of enterprises. In the cloud model,
To maintain data security and enterprise are responsibility of service providers.
All business programs strictly follow Service
level deals. A key role is played by Functional
teams in management of service level deals
and runtime establishment of programs. In
Production environments, functional teams
encouragement proper clustering and Fail over
Data reproduction, process monitoring,
Maintenance failure, restoration volume and execution control.
Despite there being many cloud sources, the
executives of platform and sub structure is still in its early stages. For example ÅAXWR-scalin‟ g is a critical need for lots of organizations.
There are huge resources to better on the
measurability and charge balancing points required today.
In various European countries, authority
regulations do not allow consumer's personal information and distinct diplomatic information to be physically discovered exterior the state or country. The arrangement
for such requirements, cloud providers required to arrange a data storage site entirely
within the country to follow with laws. This variety of sub structure may not always be probable and is a large challenge for cloud providers.
of disclosing their data in an un‐trusted
environment. In total, companies and
government operations are limited by data
control involves to introduce their application and/or data within fixed geographic limitations. This appoints for hybrid cloud environments that can seamlessly task together, where components of the application can be hosted in a public cloud and other
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 8, August-2013 1888
ISSN 2229-5518
components such as data is hosted on establishment.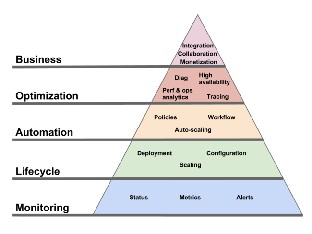
7.2 software revises:For the most part of the computer specialist spend lots of their time and creation downloading distinct variants of software so that they
can approach the distinct programs and data with brief efforts. It is not necessary to download that particular software.
is no more required, so there is limitless on entertainment choices. Uploading modish software and purchasing events from the market outlet is going to be goods of the olden days. In the upcoming
days, there will be mobile 3D games to
entertain for kids.
inclusion, it will create comfortable the activity of data handling.
that with enhanced cover up of computing
all over the Internet it is here the performance of cloud computing can play
a considerable character supplying
IJSER © 2013 http://www.ijser.org
International Journal of Scientific & Engineering Research, Volume 4, Issue 8, August-2013 1889
ISSN 2229-5518
Interoperability.
training on the doorsteps of students over an boundary.
appearance of mobile phones the idea of conventional wallets has proceed for through. Now everything correct from your connection lists to your purchasing connected requirements and you air ticket
for trips to clicking the images of pleasant
instants, everything can be completed by you mobile smart phone. The cloud is the
cause of its promising.
huge organisations. Contrasted to locally
server programs a cloud compound would provide enterprise elasticity and scope that anyworld ²wide corporation would dissatisfaction. This is specific convincing,
and on among events, this aspect can be the unique logic for an organization to migration into the cloud.
fun in the organisation.
but also the progressing day ²to- day of their public cloud computing environment. In current days everything is moving to the cloud and
it is constructing a lowest and optimum path to accomplish requirements of customers and satisfy them by customize it in best way according to their needs. Cloud computing has some security related issues but it overweigh over its drawbacks.
[1]-Birman, K., Chockler, G., and van Renesse, R. 2009. Toward a cloud computing research agenda. SIGACT News, 40, 2,
[2]-Gupta, Vinita. (2008, November 17). Will
Cloud
Computing really take off? Retrieved June 03,
2009 from
[3]http://www.expresscomputeronline.com/2
0081117/management01.shtml
[4]-´EC2 ZHE VLWH,µ
http://aws.amazon.com/ec2/. [From Amazon
EC2's web site: "Amazon Elastic Compute
Cloud
(Amazon EC2)".]
[5]-CORXG SHFXULW\ AOOLDQFH, FSHFXULW\
Guidance for Critical Areas of Focus in Cloud
Computing V2.1‖ , Cloud Security Alliance,
2009.
[6]-D. BERNSTEIN, E. LUDVIGSON, K.
SANKAR, S. DIAMOND,
M.MORROW, Blueprint for the Intercloud
² Protocols and Formats for Cloud Computing
IJSER © 2013 http://www.ijser.org